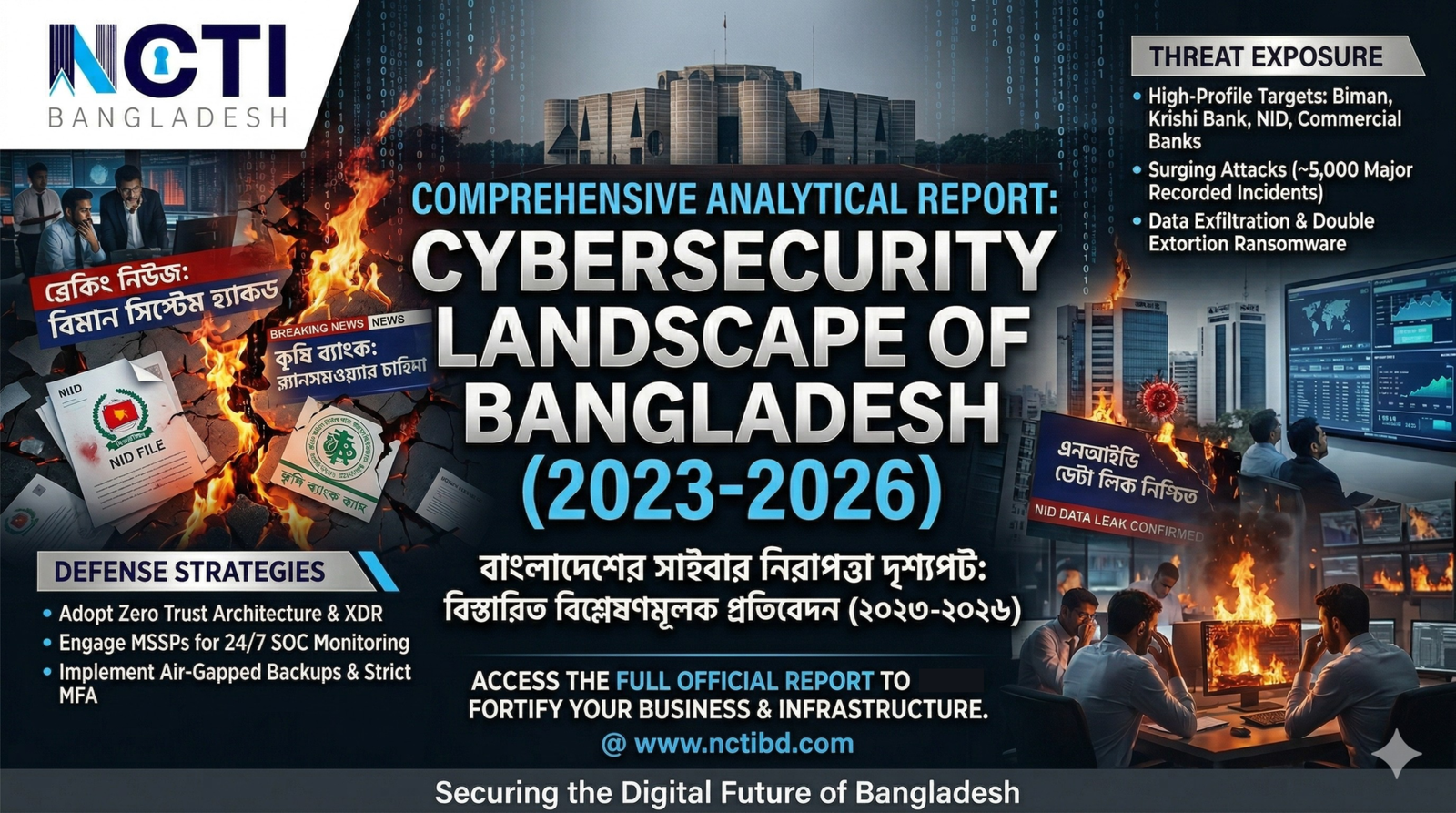
The digital landscape in Bangladesh is evolving at a breakneck pace. As of 2026, the country has transitioned from being a “soft target” to a high-stakes arena for global threat actors. For Bangladeshi companies, the “Smart Bangladesh” vision brings not only opportunity but also a sophisticated breed of digital peril.
The State of Cyber-Risk in Bangladesh: 2026 Analysis
Bangladesh currently faces a dual-threat environment. Internally, the rapid adoption of digital banking and e-governance has outpaced the development of security protocols. Externally, geopolitical shifts have made Bangladeshi infrastructure a testing ground for state-sponsored groups and organized financial cartels.
Why Now? The Drivers of Vulnerability
- AI-Weaponization: Attackers are now using generative AI to create hyper-realistic phishing campaigns in Bengali, bypassing traditional “bad grammar” filters.
- Legacy Debt: Many industry leaders are still running core operations on unpatched, decade-old hardware.
- The “Hardware-First” Fallacy: Historically, 95% of IT budgets in Bangladesh went to physical infrastructure (servers, PCs), leaving less than 5% for the “invisible” layer of cybersecurity software and talent.
Top 20 Bangladeshi Companies at High Risk
The following list represents companies that are critical to the national economy. Their “risk” is not necessarily a reflection of poor management, but rather their high-value data, critical infrastructure role, or vast customer reach, which makes them “Crown Jewel” targets.
| Rank | Company / Institution | Sector | Primary Risk Driver |
| 1 | Bangladesh Bank | Central Bank | State-sponsored financial espionage. |
| 2 | Grameenphone | Telecom | Mass data harvesting of 80M+ users. |
| 3 | bKash | MFS | Fraudulent API exploitation & credential stuffing. |
| 4 | Sonali Bank PLC | Banking | Legacy system vulnerabilities in state-owned infra. |
| 5 | Robi Axiata | Telecom | High exposure through 5G network integration. |
| 6 | City Bank PLC | Banking | Target for sophisticated ATM/Swift-based heists. |
| 7 | Dutch-Bangla Bank (DBBL) | Banking | Largest ATM network vulnerability. |
| 8 | Nagad | MFS | Rapidly scaling digital footprint with high cash-flow. |
| 9 | Banglalink | Telecom | Vulnerability in third-party vendor supply chains. |
| 10 | BRAC Bank | Banking | SME and retail data security. |
| 11 | IDLC Finance | NBFI | Sensitive corporate financial records. |
| 12 | Summit Communications | Infrastructure | Gateway/Fiber-optic backbone disruption. |
| 13 | Daraz Bangladesh | E-commerce | Payment gateway and customer PII theft. |
| 14 | Islami Bank (IBBL) | Banking | Largest private sector liquidity target. |
| 15 | BEXIMCO Group | Conglomerate | Industrial espionage across diverse sectors. |
| 16 | Bashundhara Group | Conglomerate | Operational Technology (OT) risks in manufacturing. |
| 17 | Square Pharmaceuticals | Healthcare | Intellectual property & formula theft. |
| 18 | DESCO / DPDC | Power/Utility | Critical infrastructure (Grid) disruption. |
| 19 | Pathao | Tech/Logistics | Real-time tracking data and user movement logs. |
| 20 | Chaldal | E-commerce | Supply chain disruption and logistics hijacking. |
Why Attacks Will Surge in the “Nearest Future”
The risk is no longer theoretical. In the coming 12–24 months, we expect three major catalysts for cyber incidents:
- The “Deepfake” Social Engineering
Attackers are moving beyond emails. We anticipate “Voice Phishing” using AI to clone the voices of CEOs or CFOs to authorize urgent fund transfers. For a culture like Bangladesh, where “authority-based” instructions are rarely questioned, this is a systemic risk.
- Supply Chain Contamination
Instead of attacking a bank directly, hackers are targeting the smaller software firms that provide the bank’s ERP or HR modules. One “poisoned” update can compromise dozens of corporations simultaneously.
- Ransomware 2.0 (Double Extortion)
It’s no longer just about locking files. Hackers now steal the data first, then threaten to leak sensitive customer information to the public or regulators unless paid. For Bangladeshi firms, the reputational damage is often more expensive than the ransom.
The “Golden Strategy”: A Common Suggestion for All
Regardless of the sector, every major Bangladeshi firm must move from a Reactive to a Resilient posture.
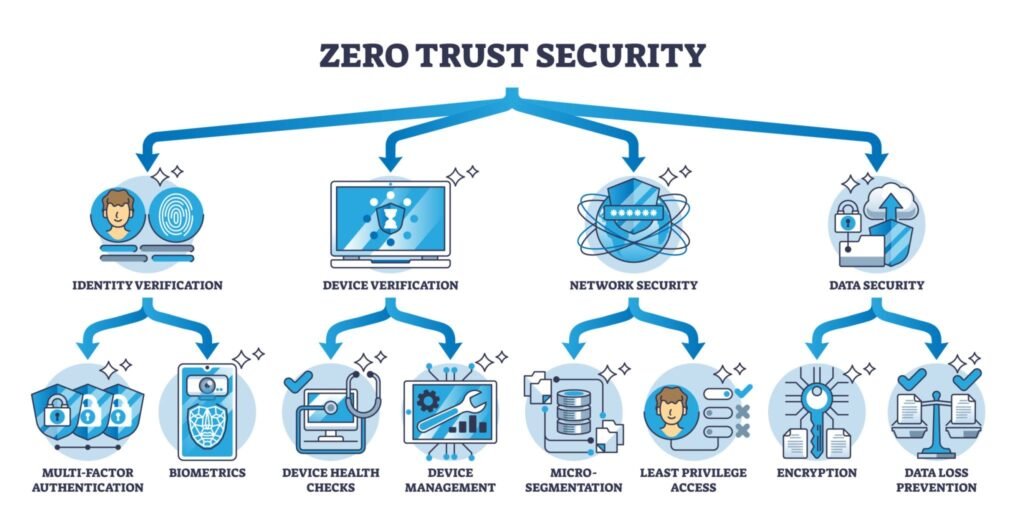
The Recommendation: Adopt the “Zero Trust” Architecture.
In a “Zero Trust” model, the system assumes that every user, device, and network—even those inside the office—is a potential threat.
- Implement Multi-Factor Authentication (MFA): This is the single most effective barrier against 90% of current attacks.
- Segment the Network: Ensure that if a hacker gets into the “Canteen Wi-Fi,” they cannot jump to the “Core Banking Server.”
- Continuous Awareness: Cybersecurity is 20% technology and 80% people. Regular “Phishing Simulations” for employees are mandatory.
Final Thoughts: The Cost of Inaction
In 2026, cybersecurity is no longer an “IT issue”—it is a Boardroom issue. For the top 20 companies listed above, a single major breach could lead to a loss of public trust that takes a decade to rebuild. The companies that survive the next five years will be those that treat security not as a cost center, but as a competitive advantage.